Security at NPLAN
Supply chain data available and secure, anywhere, anytime. Dedicated cloud hosting, end-to-end encryption, continuous auditing and enterprise-grade AI governance.
Authentication
Active Directory integration and Single Sign-On (SSO) via Google or Microsoft, aligning NPLAN with the organization's identity and security policies.
Cloud
Single Tenant SaaS hosted on Microsoft Azure. Default deployment in Brazil South, with other regions available to reduce latency and meet data residency requirements.
Privacy
Compliance with LGPD (Brazil), GDPR (European Union) and PDPA (Latin America), protecting personal and sensitive data across the full lifecycle.
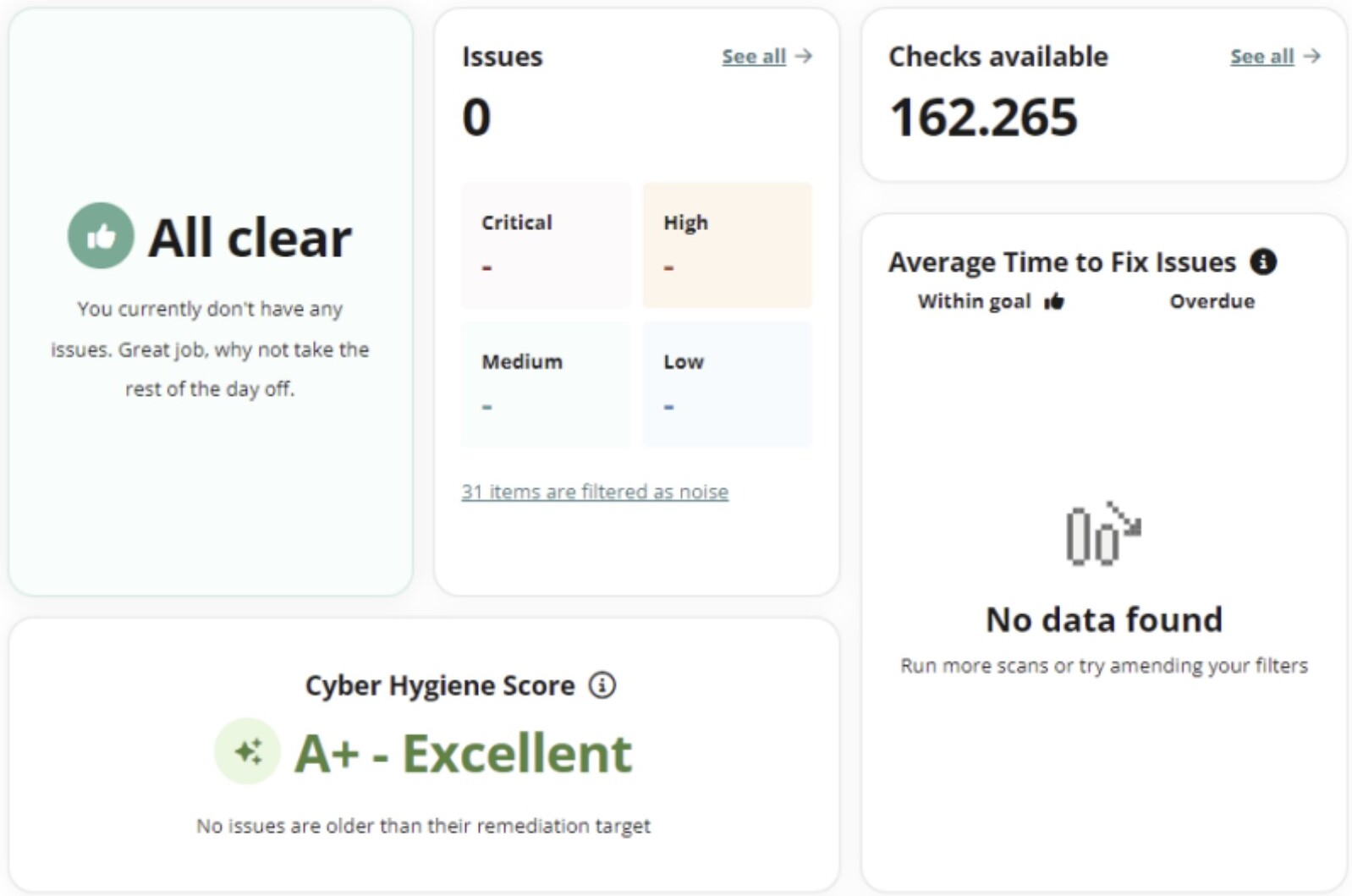
Continuous security auditing
Regular penetration testing audits evaluate thousands of vulnerabilities to ensure robust protection. Audits are carried out by Intruder Systems Ltd, an independent company specializing in continuous security monitoring for web applications and infrastructure, CREST member, monitored by Drata for SOC 2 compliance and Cyber Essentials certified.
Vulnerable software & hardware
Web servers (Apache, Nginx), mail servers (Exim), development software (PHP), monitoring (Zabbix, Nagios), network systems (Cisco ASA), CMSs (Drupal, WordPress) and known vulnerabilities such as Log4Shell and Shellshock.
Web application vulnerabilities
Coverage of OWASP Top Ten: SQL Injection, XSS, XXE, local/remote file inclusion, server misconfigurations and unintentionally exposed content.
Attack surface reduction
Identification and mitigation of publicly exposed databases, administrative interfaces, sensitive services (SMB) and monitoring tools unnecessarily reachable from the internet.
Information leakage
Detection of data that could assist further attacks: local directory paths, internal IP addresses and verbose error messages.
Encryption weaknesses
Review of SSL/TLS implementations against Heartbleed, CRIME, BEAST, ROBOT, weak ciphers, misconfigured certificates and unencrypted protocols such as FTP.
Common mistakes & misconfigurations
Misconfigured VPNs, exposed SVN/git repositories, unsupported operating systems, open mail relays and DNS allowing zone transfer.
Disaster Recovery Plan
Our DR plan ensures business continuity and data security, providing robust protection against unexpected failures.
Rapid recovery
RTO (Recovery Time Objective) of 4 hours and RPO (Recovery Point Objective) of 24 hours in the standard package.
Automated backups
Daily backups stored in redundant, geographically dispersed data centers.
Security and compliance
Data encrypted in transit and at rest, compliant with global standards such as ISO 27001 and GDPR.
Routine testing
Semiannual recovery system tests, with outcomes used to continuously improve the plan.
Encryption
All sensitive data is encrypted in transit and at rest using advanced algorithms such as AES-256. Protocols are updated regularly, with robust key management practices safeguarding encryption keys.
Granular access and permissions
Access to executions, planning modules, data menus and tables is meticulously controlled by user groups. Granular control allows limiting access to specific data rows based on user roles, enhancing privacy and regulatory compliance.
AI with enterprise governance
NPLAN does not use standalone AI services. The Gen-AI layer runs on Azure OpenAI, in a secure Microsoft environment, with guaranteed data residency, customer data excluded from training, simplified audits and an enterprise 99.9% SLA. Companies that take supply chain seriously cannot expose operational, commercial and strategic data to public models. Gen-AI usage in NPLAN follows a different standard from casual use.
AI models used through dedicated enterprise contracts (Azure OpenAI). Data is not used for training and remains under company control.
Guaranteed data residency: information never leaves the country of deployment. In Brazilian deployments, data stays in Brazil.
Controlled dataset access: the model receives only the context required for the question; full data access happens in a structured, local manner.
Protection layer that blocks sensitive information from being sent in prompts (margins, financial data, strategic info), with rules configurable by IT.
AI agents call deterministic engine functions: calculations, rules and validations remain auditable. AI orchestrates, it does not replace the engine.
Every AI interaction is monitored and logged: prompts, responses, executed actions and response time are available for audit.
Traceability
The solution keeps detailed logs to provide comprehensive security control:
- Successful and failed login attempts
- Access to screens, pages, reports and dashboards by user
- Integration activities, successful and unsuccessful
- Manual data or parameter changes, with user, date and revert capability
NDA Agreement
Both the NPLAN team and deployment partners sign a Non-Disclosure Agreement (NDA), a standard clause in all project contracts, ensuring information confidentiality. Transmission or handling of customer data by external partners is strictly prohibited.